“Information warfare refers to the conflict between two Information or more groups in the information environment. The main purpose of information warfare is the deletion of critical information. It is performed by insiders, terrorists, hackers, criminals, etc. The target of information warfare is to gain information superiority.”
Types of Information Warfare
- Information Warfare at Personal level
- Information Warfare at Corporate Level
- Information Warfare at Global Level
1. Information Warfare at Personal level
The information warfare at a personal level refers to the act of obtaining personal information of an individual without his permission. This warfare aims at the privacy of a person. This warfare aims at stealing a person’s identity and launches the attack against at stealing an individual’s digital privacy.
Nowadays mostly all the personal information is stored in digital form and individuals have very less control over the information. Personal information is distributed across thousands of computers and databases.
The information obtained by industries could be used for various malicious activities such as blackmailing, destroying the integrity of a person, ruining the reputation, misusing the information for financial transactions etc.
The methods used for personal information warfare are:
(I) Malware attacks
(II) Removable media
(III) Password cracking
(IV) DoS (Denial of Service) attacks
(V) Misuse of wireless networks
(VI) Back doors
(VII) DNS attacks
(VIII) Hacking
2. Information Warfare at Corporate Level
The corporate level information warfare occurs between companies or corporation. It aims at the information stored or it may target the image or reputation of the company which can be affected in numerous ways.
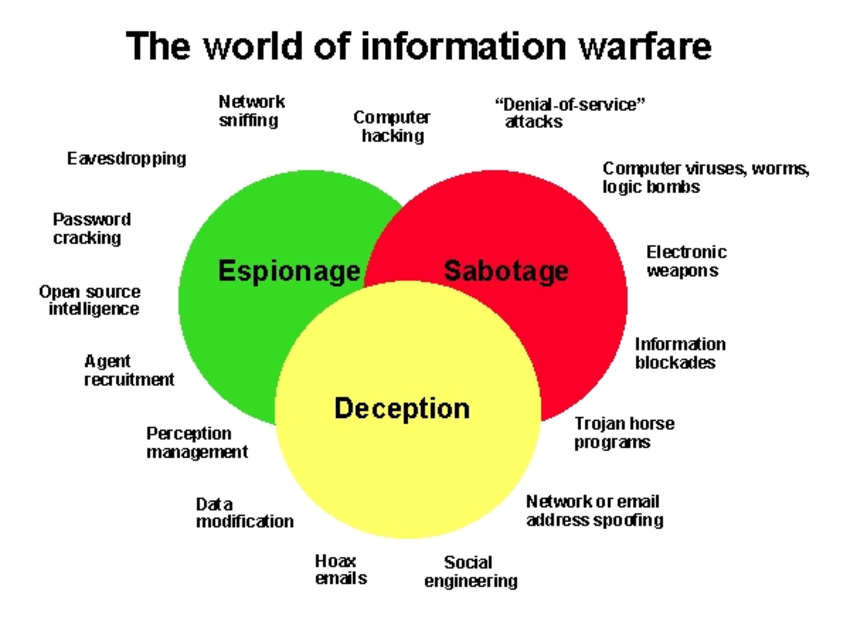
It attacks the financial and operational interests of corporations, government departments, universities and so on. Such attacks include industrial espionage, theft of services or money and sabotage.
A company can also destroy the database of competitors. Competitor’s corporate computers are hacked by the industries and all the sensitive and valuable information is stolen.
The methods used for corporate information warfare are:
(I) Website defacement attacks
(II) Malware attacks
(III) Removable
(VI) DoS (Denial of Service) attacks
(V) DNS attacks
(VI) Hacking into competitor’s computer
(VII) Semantic attacks
3. Information Warfare at Global Level
Information warfare at the global level occurs between states or countries. It aims at stealing a national security secret. The main concern in this warfare is terrorism sometimes termed as Information terrorism.
Global information warfare includes acquiring national security secrets of the country and misusing these secrets. The results of global information warfare are catastrophic.
Common methods which are used for global information warfare are:
- Website Defacement: Website defacement refers to the unauthorized modification of the content of a website.
- Semantic Attacks: Semantic attacks aim at modifying the meaning of the information. This misinformation can have a great impact.
- DNS Attacks: A terrorist group can replace the legitimate IP address associated with a domain name by the malicious IP address.
Other methods or tools used for global information warfare are:
(I) Removable media
(II) Malware attacks
(III) Hacking
(VI) Logic bombs
(V) Keyloggers
All types of information warfare are attractive options because the methods used for information warfare at all the three levels are cheap as compared to the cost of developing and maintaining military capabilities.