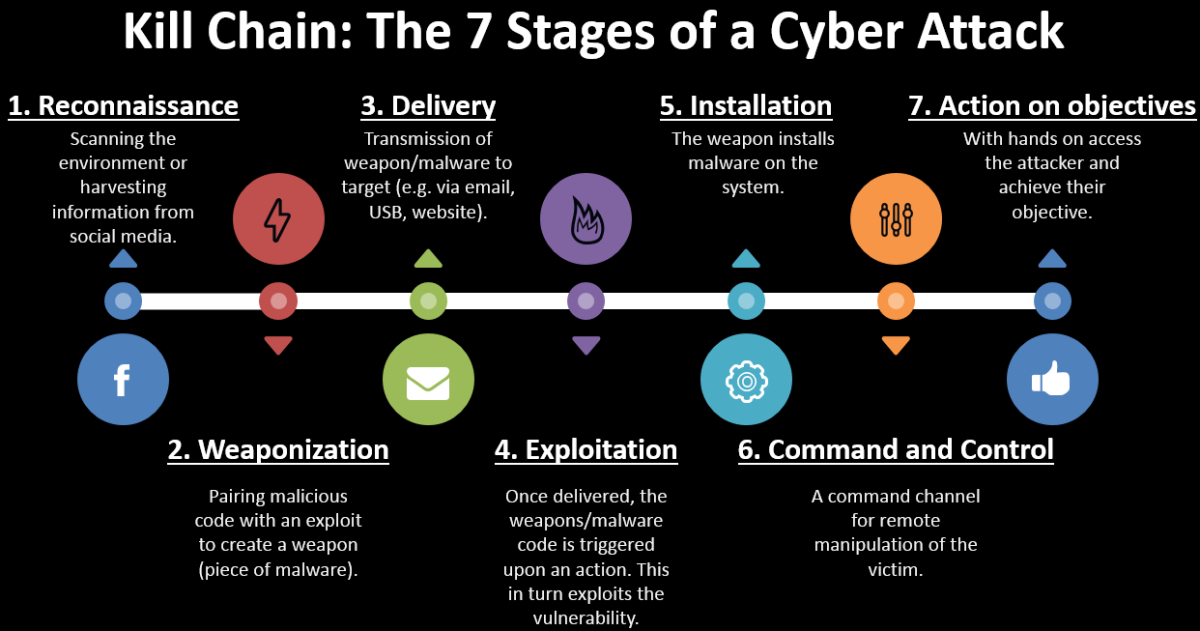
7 Various Stages of a Cyber Attack:- Cyber attacks can range from installing Spyware on a computer to attempt to destroy the infrastructure of entire nations.
7 Various Stages of a Cyber Attack
Following are the various stages of a cyber attack :
1. Reconnaissance
2. Weaponization
3. Delivery
4. Exploitation
5. Installation
6. Command and Control
7. Actions on Objectives
1. Reconnaissance
In the first stage, the attacker will reconnoiter the target’s networks and systems, looking for known vulnerabilities that can be exploited as a means of entry.
2. Weaponization
Once the target has been surveyed and the detailed objectives are understood, the attacker will prepare the software tools required to achieve them. This may involve the modification of existing commodity tools or in extreme cases the development of specialist bespoke tools.
3. Delivery
The attacker will now upload the tools onto the target system or systems, or to a targeted user, checking that they are hidden from both normal view and from detection by more sophisticated means. Delivery could be as simple as loading it onto a USB memory stick that will be found by or given to a user, attaching the malware to an email, placing it on a social media website or in a ‘watering hole’ website.
4. Exploitation
The attacker needs to be certain that the final attack will be successful, so known vulnerabilities on the target system will be exploited in order to execute the malware.
5. Installation
Having gained access to the target system or systems, the attacker will now install the malware. Often the malware suite will contain additional code to ensure that it cannot be deliberately removed, and may also be time-stamped by the attacker so that it appears to blend in with other legitimate operating systems or application software.
6. Command and Control
Having verified that the tools will work as expected, the actual attack can be executed, by possibly choosing the most appropriate moment, for example when many of the security support staff are not at work; or by staging a major diversion, which will draw attention away from the real attack.
7. Actions on Objectives
Now the attacker can begin the real work, which may be to harvest user credential information, to escalate privileges so that they can gain access to systems currently out of reach, to exfiltrate other, or simply to modify, delete data or destroy systems.